Jan 14, 2021 | Business Continuity
Why MSP relationships fail A lot of SMBs opt for managed service providers who can help handle their IT requirements, and for the most part, it works well. Almost everyone knows the benefits of having a MSP manage your IT. Increased cost savings, ability to focus on... 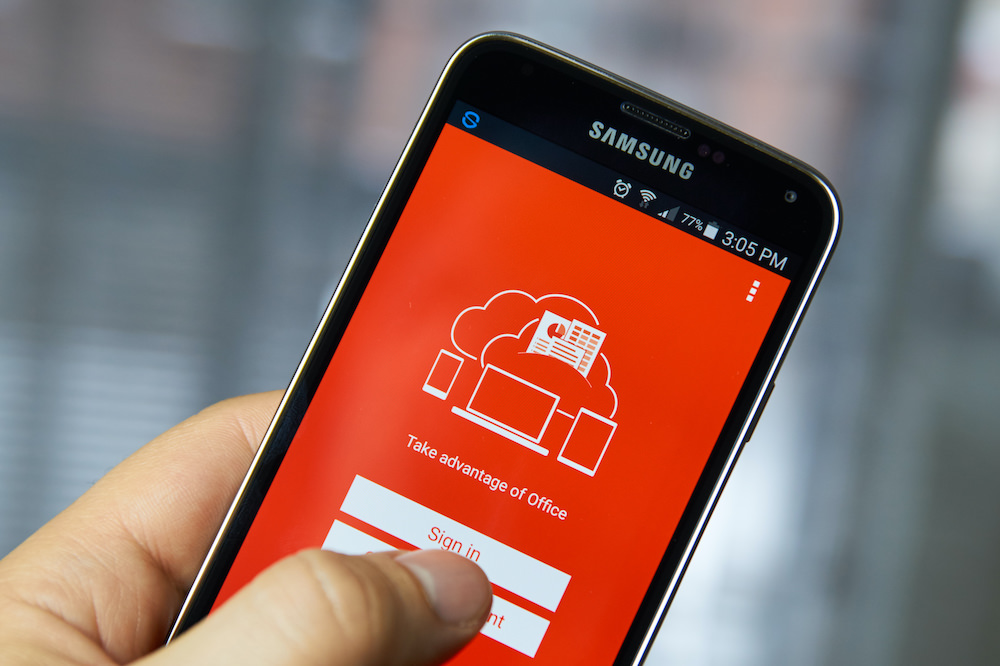
Jan 12, 2021 | Business Continuity
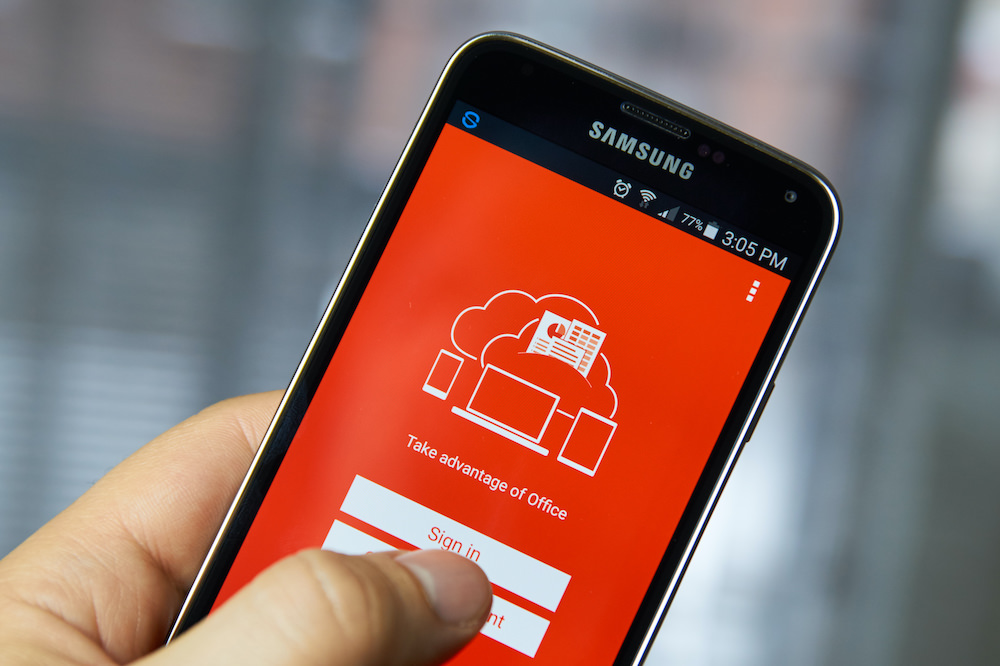
Over the past years, Wahaya IT has helped many businesses switch to Microsoft Office 365. With over a million companies using the platform worldwide, Office 365 is one of the most popular business software platforms on the market. suitable for small organizations to... 
Dec 31, 2020 | Business Continuity
Do your homework: 3 things to do when looking for an MSP Thinking of hiring a Managed Service Provider, but not sure how to go about it? Here are a few things to do before you zero in on one. 1. Figure out what you have already. The first step in a good plan is to... 
Dec 24, 2020 | Business Continuity
5 LESSER-KNOWN BENEFITS OF CHOOSING THE CO-MANAGED IT MODEL Even companies with IT staff on their payroll can’t deny having an MSP like Wahaya IT, onboard offers benefits that exceed what they get from having just an in-house team. This blog explores five lesser-known... 
Dec 17, 2020 | Business Continuity
Four reasons to opt for the co-managed IT services model The co-managed IT services model is one in which the business has its own IT team but still contracts with an external managed services provider for certain services. In this blog, we discuss four benefits of a... 
Dec 14, 2020 | Business Continuity
An excellent in-house IT team can fulfill many business needs, but they may reach a point where time and expertise are limited. In addition, internal staff can quickly become overwhelmed with special projects, needed upgrades, and additional tasks that become...